Introduction
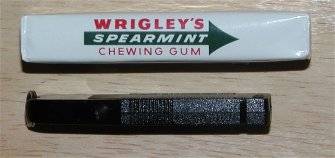
Eutron is an e-technology company specializing in Internet security hardware and software. Amongst their security measures is the PicoDisk Crypto. The PicoDisk is a USB Hard Drive (Pen Drive) similar to those that have been looked at here before. But there are two striking features of Eutrons PicoDisk Crypto that set it apart from the other brands. First, as the name “Pico” suggests (“pico” is a mathematical prefix used in the SI (metric) units system of measurement. It means 10-12) this thing is positively puny. For reference, you can see the PicoDisk shown next to a US quarter in the picture below. A quarter is 1 inch in diameter (or 2.54 centimeters for our friends across the water). This is by far the smallest pen drive that weve played with.
The second significant feature is the 128-bit encryption embedded in this device. A key code must be entered to access the data stored on this drive, providing a significant level of security for those with security needs. Note too that Eutron also makes an non-encryption model, entitled PicoDisk (without the Crypto).
Packaging
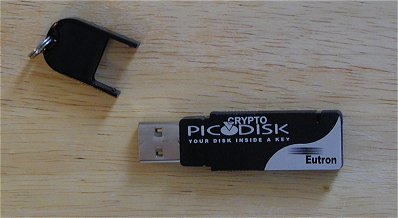
The package includes a PicoDisk Crypto, a protective cap for its USB connector, a user manual, an installation floppy disk, label, and a warranty card. Shown below are the manual, PicoDisk Crypto and the driver disk. Unfortunately, we didnt receive the cute key chain shown in the picture on the box. 🙂
The following is a detailed list of the technical specifications of the PicoDisk.
Tech Specs:
- USB spec. 1.1
- 1 LED
LED on: PicoDiskCrypto connected and enumerated
LED blinking: Data receiving or transmitting - Data transfer rate:
read (PicoDiskCrypto from Host): 700 kbyte/sec
write (Host to PicoDiskCrypto): 350 kbyte/sec - Dimensions: 60x17x7 mm
- Weight: 12 g
- Regulatory compliance FCC class B, CE
- USB bus powered (4.5 V to 5.5 V)
- Encryption algorithm: AES (performance: ~ 16 MBytes/sec on Intel Pentium II 400MHz machines)
Features:
- a fully encrypted USB drive where files and folders remain encrypted even after their use
- fast, secure symmetric encryption algorithm (AES, 128 bit key length)
- on-the-fly encryption: the user is unaware data are protected and can interact with them as he would normally do; however each time he accesses them, information is automatically decrypted in the memory by the driver
- automatic encryption of data on their transfer from an external source to the key
- CryptoPIN protection: whenever the user plugs or unplugs the key he is prompted to enter the PIN to unlock the token and further proceed with encrypt/decrypt operations while reading/writing files.
- PUK security feature: the system comes with a PUK number, a secret code to keep aside for future reference in case the PIN needs changing or has been forgotten
- easy portability: slip it in a pocket or hang around the neck
- no cables, no power supply
- compact size and light weight
Uses:
- Store securely your most valuable information.
- Transfering of files greater than 1.44MB in size between PCs that are not on a network.
- Used to replace the floppy drive on a notebook thus significantly reducing its weight.
- In enviromental conditions that cause unreliable operation of floppies and other removable media, the PicoDisk Crypto offers a fast, small, reliable alternative.
- Professionals who perform work at both office and home, find that the PicoDisk Crypto eliminates slow, unreliable, and fustrating e-mailing of large files.
- Store MP3 files on an extremely portable device.
Product Description
The PicoDisk Crypto is a small, flat, rectangular device with a black and silver plastic housing and a protective cap covering the USB connector. The cap has a small ring for attaching the device to a key chain.
This is easily the smallest flash drive I’ve tested or seen to date. It’s close in size to Transcend’s JetFlash USB Flash Drive but thinner and flatter. You certainly could put this on a key chain without adding much bulk to your key ring at all. It would nearly get lost on your pocket or briefcase/backpack.
128-Bit AES Encryption
When it came time to look into the encryption that the PicoDisk Crypto included, we turned to a friend who is better versed on the subject than we are. It ends up that he was so well versed in it that we let him clue you in on the subject himself!
Jim “Slagenthor” Patterson
Background:
The PicoDisk Crypto uses the AES algorithm with a 128 bit key length. So, what does that really mean for you the consumer?
AES is an acronym for Advanced Encryption Standard. The AES development was started in 1997 by the United States’ National Institute of Standards and Technology ( NIST ) to produce a symmetric key encryption algorithm, i.e.: one that uses the same key for encryption and decryption, for use in sensitive ( unclassified ) applications. AES was slated to replace the aging Data Encryption Standard ( DES ) which was adopted as a Federal Information Processing Standard ( FIPS ) in 1976 based on a modified version of the IBM-developed LUCIFER algorithm. Since then, DES went on to become the de-facto standard for encrypting information in many sectors of business and government, being adopted by ANSI and ISO along with large parts of the banking industry.
In the last decade or so, DES has grown long-in-tooth to the point of needing replaced for two main reasons:
- It’s not optimized for modern processing devices, being first developed in the era of 4 bit micros, it works reasonably well in hardware implementations, but is notoriously inefficient in software, needing a relatively large amount of memory to function reasonably.
- Modern hardware has become fast enough to make brute-force cracking attempts, where the attacker exhaustively tries all possible keys until they recover the original message, feasible in a realistic amount of time.
For these reasons, particularly the latter, the AES development was started in the mid-nineties. NIST held an evaluation of 15 encryption algorithms in 1998, and with the help of the cryptographic research community, winnowed these fifteen candidates down to five finalists: MARS, RC6, Rijndael, Serpent, and Twofish. Out of these five, NIST selected Rijndael ( pronounced “Rain-Dahl” ) to be the AES algorithm.
All of the final candidates were comparable in terms of security. What really separates Rijndael from the others is its performance in restricted-space environments, such as the PicoDiskCrypto, that are limited in processing power and storage reserved for running the encryption operation. NIST evaluated the candidates’ performance on several platforms including older 8 bit microprocessors, Field-Programmable Gate Arrays ( FPGA ), Digital Signal Processors ( DSP ) along with 32 and 64 bit CPU’s. In general, the Rijndael algorithm had a higher throughput of encryption operations and took fewer clock cycles to do them compared to the other candidates. Also, perhaps more importantly for small, embedded applications like the PicoDiskCrypto, Rijndael doesn’t take up a great deal of memory while it is running, on the order of a couple kilobytes, and on some platforms ( Motorola 6800-class ) is more than twice as fast as the next fastest algorithm ( Twofish ).
So the AES algorithm is fast and efficient… What about the security again?
The AES used in the PicoDisk Crypto uses 128 bit keys. To put that in comparison we’ll look at its predecessor, DES.
DES uses 56 bit encryption keys, which means there are 2^56 or roughly 7.2 E+16 ( 7.2 X 10^16 ) possible combinations. 72 quadrillion sounds like a big number, and it is, but when you have a lot of resources to throw at it, it’s not as big as it sounds. In the early nineties, the U.S. Government quietly withdrew support for the use of DES for securing unclassified communications, a step implying that it no longer considered DES outside the reach of well-supplied adversaries. Then, in 1998, perhaps the final nail in the coffin, the Electronic Frontier Foundation, with a team led by John Gilmore, constructed a dedicated DES-cracker machine, nicknamed “Deep Crack” for $230,000. Deep Crack could test over 90 billion DES keys per second, running through the entire DES key-space in a few dozen hours. It’s widely believed that certain agencies of the U.S. government have had DES crackers since the inception of DES, but now that capability is available to nearly everyone. Of course, if your information only needs to be secure for a short time, then DES would still work for you.
To compare this to the effort and time needed to brute-force a 128 bit symmetric key, if you had a device that could test the equivalent of the entire DES key space, 2^56 keys, every second, it would still take on the order of 100 trillion years to cover all 2^128 combinations. Keep in mind that the Universe is only about 15 billion years old.
So, the brute-force attack is out for now, what about other methods? Recently an attack on the Serpent and Rijndael algorithm was published by two researchers who claim to break the Rijndael in less time than it takes to do a brute-force attack. Bruce Schneier, perhaps the best known American cryptographer, founder of Counterpane Internet Security, and developer of the Twofish algorithm, wrote an article about this attack. To sum it up, he makes the distinction between types of “cracking”: the mathematical crack and the engineering crack. To the Mathematician, an algorithm has been cracked if you can recover the key in less time than it takes to brute-force the key; whereas to the Engineer, an algorithm isn’t cracked until you can actually implement an attack in hardware or software that works. Schneier currently considers this new attack to, at best, be a crack of the mathematical type, if the paper turns out to be correct, but not one that can actually be implemented on real-world AES-encrypted data.
How does the AES encryption on the Pico disk work for you?
When you install your device drivers for the PicoDisk Crypto, the software installation handles the encryption for you. You are asked to select a Personal Identification Number ( PIN ) between 6 and 20 characters in length. This PIN is what you use to access the PicoDisk Crypto when it is attached to your computer. Wait a minute, you say! There aren’t 128 bits in this PIN for a crypto key. You are correct. The next step in the installation process prompts you to move your mouse cursor randomly around the screen.
What is actually occurring is that the software is using your mouse movements as a random seed for the actual AES encryption key, what the PicoDiskCrypto refers to as the PUK. You are also given the option of specifying your own PUK number. The PUK number is necessary to get a new PIN if you happen to forget your old pin. You are encouraged to write the PUK number down and store it in a safe place, because if you forget your PIN, and you don’t have the PUK number, then you will not be able to access the data stored in the PicoDisk Crypto. It should be apparent that if somebody has physical access to your PC, then they could conceivably get your PIN and/or PUK number in order to access your private data. This should remind you of the maxim of computer security: “Without physical security, there is no security”. Your data inside the PicoDisk Crypto is secure while it is out and about with you in the wide world, but you need to take reasonable steps to keep your PC secure as well.
Installation
Unlike other flash drives that weve tested recently, the PicoDisk Crypto needs drivers due to the encryption capabilities built into the drive. When you first plug it in, you are prompted that Windows has found a new USB device.
From there it will look for drivers and you can point it towards you’re floppy drive and the included driver disk. Alternately, you can pull down drivers from Eutron’s webpage and point the installer to the applicable location of the donwloaded drivers on your hard drive. This is important if you want to use your PicoDisk on a PC other than your primary one. Even if you dont have the driver disk with you you can always pull down the requisite drivers off the Net. You NEED the drivers to access the PicoDisk, to communicate with the encryption.
Once Windows accesses the drivers and begins the installation, it will prompt you for a Login. This will be your password, and you’ll have to enter it every time you plug your PicoDisk into a PC loaded with the PicoDisk software.
With Win2k that’s pretty much all there is to it. You’ve now installed your PicoDisk device, and it is ready for use!
Installing the PicoDisk to a Windows ME machine followed a similar but slightly more in depth procedure. When you plug the device in the installer will ask you to choose a PIN number and then re-enter it to confirm it. You are then prompted to move your mouse around the screen to “collect a random sequence of data necessary for initializing the PicoDisk Crypto device” as described in the section on AES encryption above. As you move your mouse you’ll see a progress bar advance and then prompt you to hit “next” when it has enough random data.
Okay, you’re almost done now but there are still a couple of more steps. The installer will then give you a randomly generated “PUK” number which is used when you forget your password . They recommend you either print this screen out or write down the PUK number. I do too. If you can’t remember your password, I don’t see how you’d ever remember this number either!
The next step is the formatting of the drive. On the 8MB version we tested this only took a few moments but might be a bit longer with larger models. After that Windows will claim it’s done installing the device and ask you to click “finish”. Once that is completed, you’ll be prompted for the final step of the installation procedure and that’s one more quick driver install for the PicoDisk Crypto storage controller.
Whew! That’s finally it! Actually it doesn’t take very long to do in practice but it is more involved than the very quick and simple Windows 2000 installation. I imagine that installation under Windows XP would be similar to the Windows 2000 procedure.
Use and Testing
Once all that’s done you can take a look at the drive in your Windows Explorer application, or My Computer. On my laptop the PicoDisk showed up as my F-drive, the next available logical drive letter after my CD-DVD drive.
A quick look at the drive properties shows the PicoDisk reading as 7.78MB, just under the 8MB listed size of the drive. Now, I noticed a similar phenominon with some of the other flash drives we tested recently but I actually found out why it happens from reading Eutron’s FAQ’s. Take a look:
Q- Why after the use of a PicoDisk-Crypto on Win 2000 or Win XP the available disk space is smaller than the effective free disk space?
A- Probably, the PicoDisk-Crypto was unplugged on Win 2000 or Win XP without the previous disconnection of the PicoDisk-Crypto device with the system utility “Unplug or Eject hardware” that you can find in the operating system traybar. To solve the problem, you can run the “Check Disk” system utility selecting the option “Automatically fix file system error” (the “Check Disk” utility is supported only on Win 98 and Win ME).
Q- Which is the correct procedure to unplug a PicoDisk-Crypto on a Win 2000 or Win XP operating system?
A- Follow these steps to unplug correctly a PicoDisk-Crypto on a Win 2000 or Win XP operating system : 1 – Select “Unplug or Eject hardware” icon that you can find next to the system clock on the operating system traybar (desktop) 2 – “Stop” the device with the specific button will appear (make sure that there are not running applications that are using the Removable Unit associated to the PicoDisk-Crypto) and the confirm message “Device can now be safely removed from the system” will appear. 3 – Now you can unplug the PicoDisk-Crypto from the USB port.
Hmm, that could well be. I have to admit I’m not always good about using the “Unplug or Eject Hardware” function before pulling USB devices free. It always seems like a tedious extra step to deal with when using an otherwise very handy piece of hardware. But, with only 8MB of storage, its worth the effort!
I tried running ScanDisk (Win ME doesn’t have a “CheckDisk” option that I can find, maybe Win 98/SE did but I can’t recall for sure) from the drive Tools area and set the “Automatically fix errors”. It made no difference that I could see as I still ended up with 7.78MB after the process was over. Perhaps Win 98/SE would have given me a different result, but I don’t have access to a 98 machine at this point.
On the other hand, on standard IDE hard drives, you typically dont always get the prescribed storage space indicated on the box either. This may also be the case for this device.
SiSoft Sandra and File Transfers
After the install, I unplugged the PicoDisk Crypto, rebooted my PC and came back to it a bit later. I plugged the PicoDisk in and was immediately greeted by the password prompt. After entering my password, the box disappeared, and you could work with the PicoDisk just as if it were any other flash drive.
For test purposes, I first ran SysMark, SiSoft Sandra’s File System Benchmark. The PicoDisk came back with a score of 612. That’s a heck of a lot faster than a floppy and even a bit faster than a ZIP drive. This compares favorably with the score of 645 that Shane got on the SanDisk Cruzer which he tested recently, although it did lag behind the 813 that Transcend’s JetFlash yielded.
Next I did some file transfers. When you start transferring files around you rapidly find out that 8MB isn’t very much space! I was able to pick two MP3 files that made up 7.5MB and used those. I also tried a 2MB selection of MS Word documents for my file tests. The 7.5MB files transferred in approximately 5 seconds whereas the 2MB files transferred over from my PC to the PicoDisk in around 1 seconds time.
Conclusion
:
While the PicoDisk worked well in our tests we feel the 8MB is almost akin to a shareware application: It lets you try out all the features of the product and see if you like it or not, but it’s a bit too limited in storage capacity to be truly useful for most people. If you’re interested in getting one, we’d have to recommend a larger size. While certainly still better than a floppy disk, 8MB is still way too small for use with any sort of multimedia files. The encryption software adds an extra step to using the device and does require that you have software installed on each computer which you intend to use the PicoDisk Crypto on, unlike conventional flash drives. However, 128-bit encryption, as weve discussed above, is a hard cookie to crack. If you are interested in a portable and secure device, this is your choice. If you only need to transfer a few secure documents or the like, the 8MB version may suit you. Otherwise, models varying from 16MB up to 512MB are available.
Were giving the Eutron Pico Disk a score of 7.0 out of 10. It worked well, has top notch security capabilities, but was god awfully under sized for broad use. The last bit being the only reason it didnt score higher. However, it does receive the Bjorn3D Seal of Approval for being pico-small and including easily used encryption.
 Bjorn3D.com Bjorn3d.com – Satisfying Your Daily Tech Cravings Since 1996
Bjorn3D.com Bjorn3d.com – Satisfying Your Daily Tech Cravings Since 1996